1. The container host operating system and multi-tenancy
2. Container content (use trusted sources)
3. Container registries (secure access to container images)
4. Security and the build process
5. Control what can be deployed within a cluster
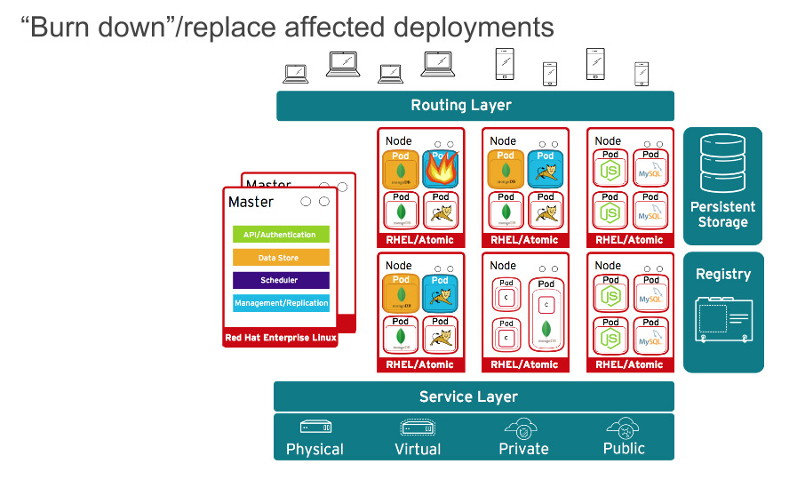
6. Container orchestration: Securing the container platform
7. Network isolation
8. Storage
9. API management, endpoint security, and single sign-on (SSO)
10. Roles and access management in a cluster federation